Shell Security Plugin
A new plugin that audits your OpenClaw instance and tells you what to fix—right in your chat.
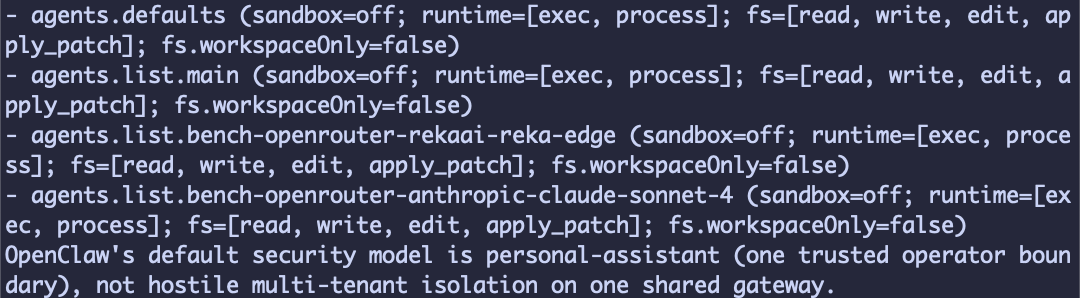
I ran openclaw security audit on my instance the other day and got back a wall of text. Six findings — one critical, three warnings, two informational. I stared at it for a minute, scrolled through the nested objects, and thought: “Okay, but what should I actually do about this?”
That’s the gap the new Shell Security plugin fills. It takes that same audit output, sends the findings (not your secrets, not your config) to the KiloCode Security Advisor API, and gives you back a prioritized report with specific remediation steps. The whole thing happens in your chat — Telegram, Slack, the Control UI, wherever you talk to your agent.
What it does
The plugin is a thin bridge between two things that already exist:
openclaw security audit — the built-in CLI command that checks your local config for common security foot-guns (weak models without sandboxing, exposed runtime tools, missing trusted proxies, multi-user setups without isolation)
KiloCode’s Security Advisor API — an endpoint that takes those findings and returns expert analysis with context-specific remediation guidance
The plugin runs the audit locally, packages the JSON output, and sends it off. What comes back is a markdown report that covers what was found, why it matters, and what to do about it — organized by priority.
Installing it
It’s currently dev-only but will be released soon!
openclaw plugins install @kilocode/shell-security
openclaw plugins enable shell-security
openclaw gateway restart
The gateway restart is a one-time thing after install. If you’re talking to your agent through Slack or Telegram, you’ll see a brief connection blip and then it’s back.
Two ways to run it
Slash command (recommended):
/shell-security
This runs the plugin directly and renders the full report. It bypasses the LLM’s summarization layer entirely, so you get the complete output regardless of which model you’re running.
Natural language:
You can also just say “run a security checkup” or “audit my OpenClaw config” and the agent will call the tool. One thing to know: if you’re running a smaller model (Haiku, GPT-x-nano), it might paraphrase or truncate the report. Capable models like Sonnet or GPT’s latest handle it fine. When in doubt, use the slash command.
First-run authentication
The first time you run it, the plugin prompts you to connect your KiloCode account through a device auth flow:
Open a URL in your browser
Enter a code
Sign in or create a free account
Run /security-checkup again
After that, the token is saved and you never see the auth flow again. There’s a gateway reload on first auth (the plugin writes the token to your config), but subsequent runs are instant.
If you’re running OpenClaw in CI or a container, you can skip the interactive flow entirely by setting KILOCODE_API_KEY as an environment variable.
What gets sent (and what doesn’t)
This matters. Your OpenClaw instance has access to your filesystem, your API keys, your chat history. The plugin doesn’t send any of that.
Sent:
The JSON output of openclaw security audit — finding IDs and summaries, no secrets
Your OpenClaw version and plugin version
Your instance’s public IP (for optional remote probes)
Not sent:
Config file contents
API keys, secrets, or tokens
Chat history
Workspace files
Everything goes over HTTPS, authenticated with your KiloCode account token.
What the report looks like
On my instance, the report came back with findings grouped by severity—the critical one about small models running without sandboxing at the top, followed by the warnings about trusted proxies and multi-user heuristics, and then the informational items. Each finding includes context about why it’s a risk and concrete steps to fix it.
It’s... a lot of text right now. The formatting still needs work—the dev release is functional but not polished. There’s also a bug where the KiloClaw call-to-action shows up even if you’re already a KiloClaw user. These are known rough edges that’ll get smoothed out before the stable release.
Why this is useful
Running openclaw security audit is already good practice. But JSON output requires you to interpret each finding yourself, look up what the check IDs mean, and figure out the right remediation. The Security Advisor layer turns those findings into specific guidance you can act on immediately.
For anyone running OpenClaw as a personal assistant (which is most of us), the security surface is real. Your agent has shell access, filesystem access, web browsing. A misconfigured model fallback or an unintended multi-user exposure means your agent could be manipulated by untrusted input. Having something that checks this and explains the results in plain language saves you from reading JSON and guessing at severity.
Current status
The npm package is live and the source is on GitHub under MIT license. A stable release is coming — the main work remaining is formatting improvements and fixing the conditional CTA logic.
Install it, run /shell-security, see what it finds. It takes about thirty seconds.